A guide on how to transition into the new ISO/IEC 27001:2022
On 22/10/2022 a new version of ISO/IEC 27001:2022 was published and renamed as "Information security, cybersecurity and privacy protection - Information security management systems - Requirements". This new version replaces the last ISO/IEC 27001:201 version.
Regarding the transition period, all organisations that wish to keep their ISO/IEC 27001 certification have three years to implement the updates from the 2022 version.
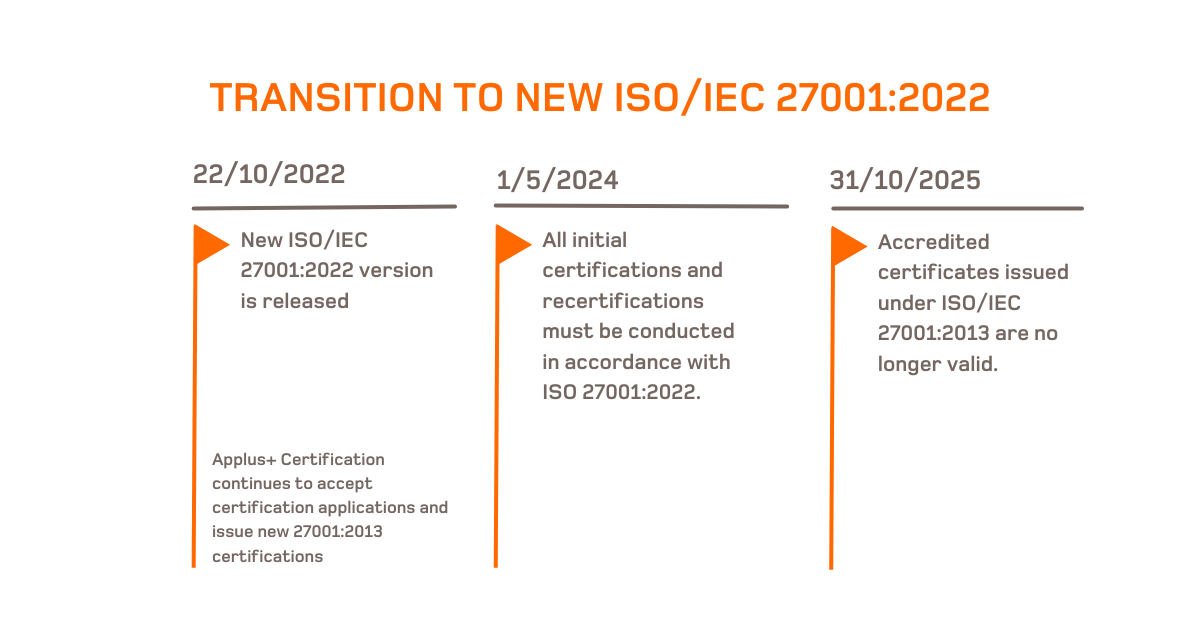
Transition calendar
These are the important deadlines that international bodies mark for the transition period of accredited ISO/IEC 27001:2013 certificates to ISO/IEC 27001:2022:
- 1 May 2024: From this date onwards, all initial certifications and recertifications must now be carried out in accordance with ISO 27001:2022.
- 1 October 2025: The transition period ends. Accredited certificates issued under ISO/IEC 27001:2013 will no longer be valid and will no longer be recognised.
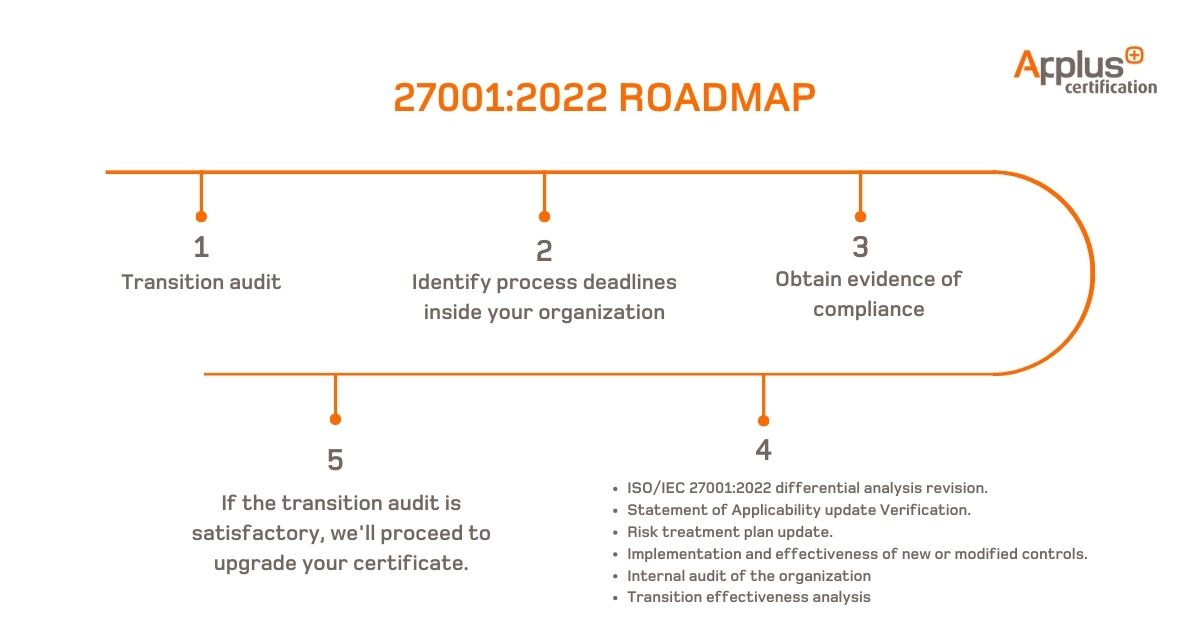
Roadmap for ISO/IEC 27001:2013 certified customers
1.To upgrade your ISO/IEC 27001 certificate to the new version, a transition audit is required. This can be done in conjunction with the planned follow-up audit, the recertification audit or through a separate audit.
2. The transition audit involves a minimum time frame set by the IAF. The times may be extended depending on the actual situation of the organisation, the size of the organisation, the performance of the management system in previous years and the complexity of the management system.
3. The transitional audit isn’t just based on the documentation review, but also requires evidence of compliance.
4. The transition audit shall include at least the following requirements:
- A review of the customer's ISO/IEC 27001:2022 differential analysis and a mandatory implementation of changes in the Information Security Management System.
- Verification of the updated Statement of Applicability.
- If applicable, an analysis of the risk treatment plan update.
- A review of the implementation and effectiveness of new controls or modified controls that have been selected by customers.
- The organisation's internal audit shall provide evidence that the new ISO 27001:2022 requirements and applicable new controls have been audited.
- The management review shall incorporate the analysis of the effectiveness of the transition.
5. If the transition audit is satisfactory (no deviations detected or after effective resolution of NCs through a PAC) Applus+ Certification shall update the certificate to refer to ISO/IEC 27001:2022 and update the version of the Statement of Applicability.
Note: The issuance and validity of the ISO/IEC 27001:2022 adapted certificated shall also consider:
- If the transition is performed with the maintenance audit: the current validity date of the certificate will be maintained.
- If the transition is in conjunction with the renewal audit: a new certificate will be issued with an effective date of 3 years.
- If the transition is performed independently: the current effective date of the certificate shall be maintained.
If you’re looking to plan the transition audit sufficiently in advance, get in touch with our Applus+ commercial team. We’re happy to provide you with more personalised information on how to move forward with this process.